
Knowledge base
Zero Trust Architecture
Explore resources on Zero Trust Architecture, a modern cybersecurity framework built on the principle of ‘never trust, always verify.’ Discover expert articles, white papers, videos, and research covering Zero Trust strategies, identity and access management, network segmentation, continuous authentication, and best practices for securing users, devices, and applications in today’s distributed environments.
Select the Categories
Select the Resource Types
Select the Resource Topics
- All Resource Topics
- Microsoft
- Cybersecurity
- Zero Trust Architecture
- MFA
- Compliance
- Email Security
- Identity Protection
- Ransomware
- wi-fi
- Broadcom
- Licensing
- AI
- Copilot
- Infrastructure
- Data Security
- Cisco
- Splunk
- XDR
- Risk Mitigation
- Healthcare
- Incident Response
- Fraud Protection
- Networking
- SASE
- Quantum Computing
- Observability
- Education
- Special Systems
- SOC
- Awards
- Cloud
- Platformization
- Security Operations
- Managed Services
- SD-WAN
- Networking & Infrastructure
- AI & Emerging Technology

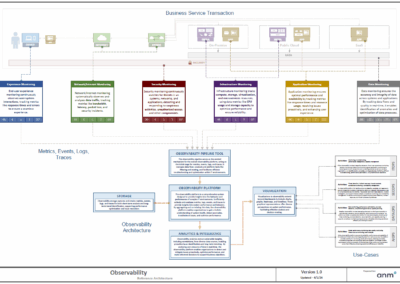
Full Stack Observability Reference Architecture

Zero Trust Architecture Services

Cyber Resilience Services

Full Stack Observability

Zero Trust in Action
Building Blocks for a Cyber-Resilient Infrastructure

Preparing for Zero Trust Adoption

Data Security Management

SASE: The New Baseline for Modern Enterprise Security

Security Platformization: Unifying Defenses in a Fragmented World

Beyond Backup: Fortify Your Data Resilience Against Cyberattacks
No results found.
